Not long ago, AI agents were harmless. They wrote snippets of code. They answered questions. They helped individuals move a little faster.
Then organizations got ambitious.
Instead of personal co-pilots, companies began to deploy shared organizational AI agents agents embedded into HR, IT, engineering, customer support, and operations. Agents that don't just suggest but act. Agents touching real systems, changing real configurations, and moving real data:
An HR agent that provisioned and de provisioned access through IAM, SaaS apps, VPNs, and Cloud Platforms.
🔹A change management agent is any agent that approves requests, makes updates to the production config, and logs those actions both in ServiceNow and Confluence.
🔹Support agent in fetching customer data from CRM, billing status check, triggering of backend fixes, and updating of tickets.
🔹These agents warrant deliberate control and oversight. They’re now part of our operational infrastructure. And in order for them to be useful, we created them to be powerful by design.
The Access Model Underlying Organizational Agents,
Traditional organizational agents are designed to operate across many resources, serving multiple users, roles, and workflows from one implementation. These organizational agents are not linked to an individual user; rather, they are shared resources which can respond to requests, automate tasks, and orchestrate actions across systems for many users. In such a design, agents are easy to deploy and scalable across the organization.
To act smoothly, these agents use shared service accounts, API keys, or OAuth grants for system authentication. Such is typically a long lived set of credentials, which is centrally controlled, enabling continuous operation of the agent without additional actions needed from a human user. To enable smooth interaction with the agent and allow handling of a broad scope of requests, rights are typically granted on a wide scope of systems, actions, or data, which would be unnecessary for a human user.
Even though this is the most convenient and widely accepted approach, these choices have the potential of creating access intermediaries that skirt the traditional bounds of authorization.
Overcoming the Traditional Access Control Paradigm,
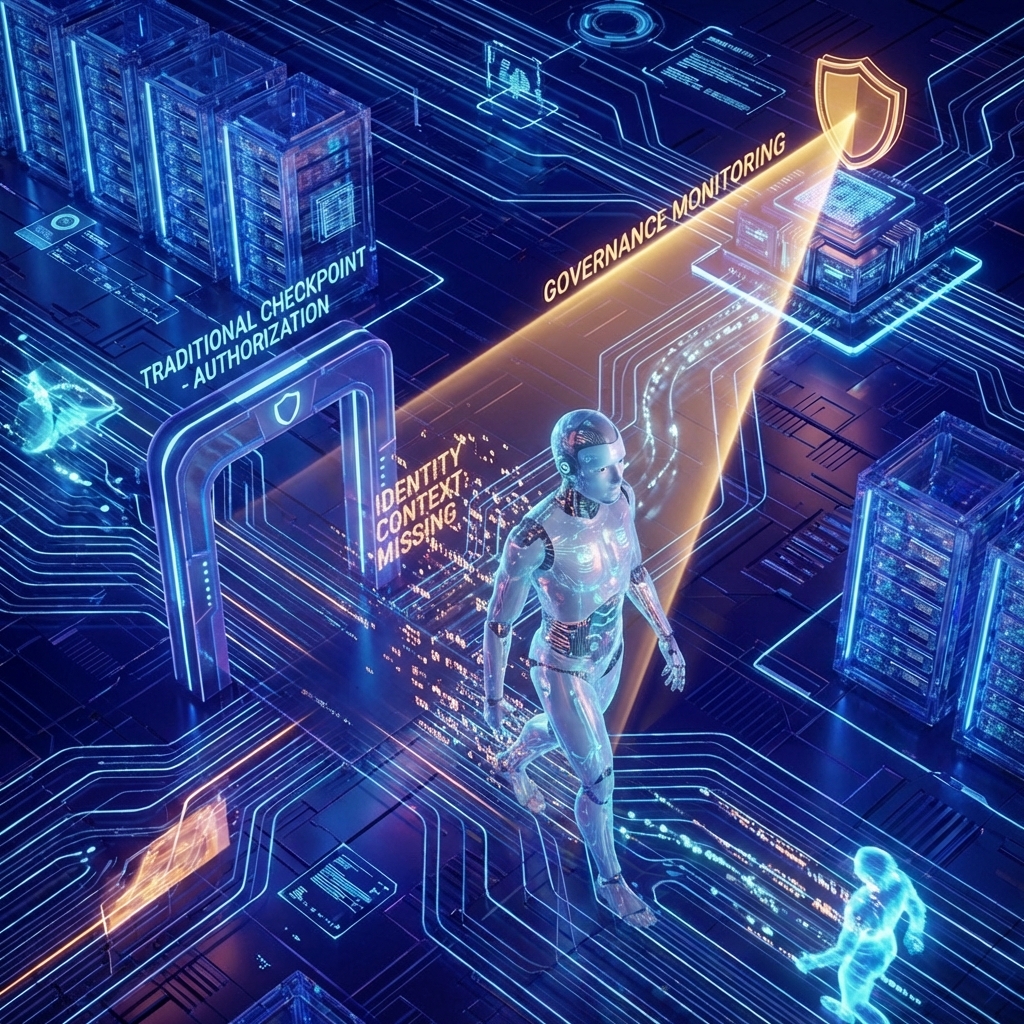
Organizational agents tend to work within or across various systems and workflows because of permissions greater than those used within other user levels. When users engage an agent within their systems, they no longer have direct access. Instead, users make a request of which the agent takes action on behalf of the user. This request and action work under the agent ID and not under the user ID. This causes disruption within traditional user control measures. A person with little user permission would be able to do or gain whatever it is they want under normal circumstances. Instead, they use an agent as a middleman and thus gain whatever it is they wish. Even though this action takes place under an intermediary ID within the logs and audit trails of security software and programs, it often occurs under non-visible observation.
Organizational Agents Can Operate Behind Access Controls,
If the agents inadvertently extend the reach of the user’s authorized access, the performed action may look authorized and innocent. Because the operation is traced back to the agent identity, the context associated with the user is erased, making attribution impossible.
For instance, when a technology and marketing solutions firm with about 1,000 workers installs an organizational AI assistant for the marketing department to evaluate customer behavior using the Databricks platform, it is given widespread access to play different roles. Otherwise, when John, a recently hired employee with restricted access, requests the assistant to perform a churn analysis, it will provide sensitive customer information that John cannot easily access.
Nothing was misconfigured, and no poilcy was broken. It just answered back based on its broader reach, which exceeded what the original company wanted.
Traditional Methods of Access Control and their Limitations in the Age of AI Agents
Traditional security mechanisms were developed with human users and direct system access in mind, and thus are not suited for agent-mediated processes. The IAM systems play a mechanism for enforcing permissions on the basis of user identity, but as AI agents perform an operation, authorization checks become dependent on the entity’s identity rather than on the requester’s. This thus renders user level limitations ineffective. The logging and auditing capabilities also pose as challenges because, as AI agents, all activity can now be traced back to their identities, thereby making it difficult for analysts to establish the initiators and purpose for action taken. Using agents, there was no ability for enforcing least privilege, misuse, or attribution, allowing for authorization by-passes that did not trigger traditional security mechanisms.
A New Identity Risk: Agentic Authorization Bypass
With the increasing number of operational tasks undertaken by organizational AI agents across multiple systems, there arises a need for security teams to gain clear visibility into the association of agent identities with important organizational entities such as sensitive data or mission-critical systems. It becomes necessary to recognize the users of a given agent and identify potential inconsistencies between the user’s entitlements and the agent’s general access, which may open up unintended authorization bypasses. In the absence of such awareness, there may remain a possibility of hidden and unchecked excessive access. The pertinent security team should focus on constantly keeping track of changes to user as well as agent permissions, which change dynamically with the passage of time as access changes.
Securing Agents' Adoption with Wing Security
AI agents are rapidly becoming some of the most powerful actors in the enterprise. They automate complex workflows, move data across systems, and act on behalf of many users at machine speed. But that power becomes dangerous when agents are over trusted, unmonitored, and unsupervised. Broad permissions, shared usage, and limited visibility can quietly turn AI agents into authorization bypasses and security blind spots.
Secure agent adoption requires visibility, identity awareness, and continuous monitoring. Wing provides the required visibility by continuously discovering which AI agents operate in your environment, what they can access, and how they are being used. Wing maps agent access to critical assets, correlates agent activity with user context, and detects gaps where agent permissions exceed user authorization.
Achieving the Adoption of Agents by Wing Security
AI agents are increasingly proving to be among the strongest players inside the enterprise. They are able to automate complicated tasks, synchronize data across applications, and perform on behalf of multiple users at machine speed. Yet their capability can be perilous if these agents are overly trusted, left unchecked, and unsupervised. Overly broad permissions, shared use, and lack of visibility can creep toward rendering AI agents authorization loopholes and blind spots.
Adoption of secure agents needs visibility, awareness, and monitoring. Wing offers the needed visibility through continuous discovery for AI agents running in your system, their capabilities, and usage. Wing relates agent access to key resources, associates agent activity with user context, and identifies gaps between user authentication and agent permissions.
👉🏻 Found this article interesting? Follow us on Facebook, Twitter and whatsapp to read more exclusive content we post.